Secure DNS: what it is and why it is important
Secure DNS is a critical component of any security service. Although we hear little about exploits via DNS, the threat is constant. In this article, we will try to clarify why it is important to know what a DNS is, how it is attacked, and what to check in order to choose the best secure DNS tool.
1. What a DNS is
The acronym DNS stands for Domain Name System and is typically compared to a phone book. In a phone book, a person’s name is associated with a phone number. In domain name systems (DNS), the IP of a computer is associated with the domain name of a site. Each computer is identified on the web by an Internet Protocol (IP), including those (servers) that contain the files that make up the internet site.
For example, the domain/site “flashstart.com” corresponds to the IP 151.139.128.11. That is, the computer hosting the “flashstart.com” site, and other sites, has that one network address. When a user decides to connect to the “flashstart.com” internet site, he types “flashstart.com” on the address bar of his browsing program (e.g. Google Chrome). His computer, however, does not understand this language; it only understands numbers. At this point it is the browsing program that instantly converts the request from a domain name to an IP address, through a service called a resolver. This address gets to the router, or gateway of a corporate network. The router, in turn, registers the IP address and sends the request into cyberspace.
From that moment on, there is a passing of requests (where do I have to go to find computer 151.139.128.11?) from one server to another, until a response is obtained. At that point, finally, the user will see the “flashstart.com” site on his browser. This sounds like a long process, but in reality the timeframe is only milliseconds long.
And, in fact, no one notices that the request went through a number of servers (hops). For example, the route from this computer to 151.139.128.11 took nine hops, of which the slowest was twelve milliseconds and the fastest–from my computer to my home router–less than a millisecond.
During the journey from the user’s computer to the server hosting the requested site, several DNSs are encountered. The so-called phone books are used to verify, at each hop, that the request by domain name matches the IP address of the server encountered on the way and not the one requested.
2. Iterative and recursive DNSs
Requests to DNS are of two types, internal and external. The internal request is made within a corporate network, or in the transition from the computer to the home router. The external one, on the other hand, occurs outside the corporate network, that is, from the moment the request leaves the home walls or the network perimeter and takes the path of the Internet. The external request still takes place and, as mentioned, this happens in the various hops until a match is found. At that point, different DNSs come into play, and the control can be iterative or recursive.
In the case of iterative DNS, the internal server – the internet provider’s server – communicates directly with each external DNS server, in turn, until it gets the server’s IP address. In the case of recursive DNS, the internal server communicates with an external “recursive” DNS server, which then communicates with other servers at the same time in order to retrieve the IP address, still from the servers it meets along the way.
In addition to a server where a DNS is hosted, a DHCP (Dynamic Host Control Protocol) server also comes into play. DHCP dynamically assigns IP addresses to new resources when they join the network. Combining DNS and DHCP results in a dynamic DNS, an essential component of any enterprise network. With a dynamic DNS, each time the DHCP server assigns an IP address to a new server, it also writes the IP address into the server’s host table so that a match (mapping) is recorded.
Without this process, an IP address would be automatically assigned to the new resources upon connection, but the server would not know they are there. As a result, someone trying to connect to the server using its domain name would not be able to do so because the server would not know where to route the request.
And it is at this point that the security issues of DNS protocol come into play.
If you have already activated FlashStart, read this guide which explains how to extend blacklists for DNS filtering on the internet.
>> FlashStart is the DNS filter that protects you against malware and unwanted contents ? Request a quotation or try it now
3. Why it is better to use a secure DNS
DNSs are not secure by definition, meaning that the DNS protocol is not asked to check whether the site being accessed is malicious. It is not supposed to check whether the requested site contains child pornography or material of any offensive nature. More than that, a priori one cannot know whether the site contains malicious elements that can trigger malware or a Trojan. Again, one cannot know if it is a phishing site.
Filtering site access requests from a corporate employee, a student in a school, someone who is browsing from a public library, or a minor is critical, not only to prevent the user from ending up on offensive sites of any kind but, more importantly, to avoid running into computer network attacks.
The vast majority of attacks on corporate networks and home computers occur after clicking on a link. The link may be contained in an email, a chat message, or a text message, and its genuineness is not verified a priori. For example, the browsing protection tools contained in Google Chrome, or internet services such as YouTube, are not enough because they are limited to protecting browsing only through that browser or on that particular service. Yet, who can protect us from clicking on a link received via email or chat?
DNS poisoning also adds to this enormous risk. This refers to specific and very widespread cyberattacks, which are, unfortunately, discussed very little. Basically, cyber criminals can modify the DNS tables contained in the servers that a request visits. The modification is simple: replace the IP address with another so that the DNS redirects to a different site than the one requested, but the DNS cannot know this!
Therefore, the importance of using a Secure DNS is obvious, a DNS service to which browsing protection is added. And how is it activated? By choosing a DNS filter. The service is inserted between the user’s request and the site and protects the user from any unpleasant surprises.
>> FlashStart protects you from a wide array of threats and blocks access to malicious sites ? Request a quotation or try it now
4. What a secure DNS service must have
A DNS filter must have certain properties related to IP-domain name association tables. A company, school, or public institution that decides to protect the browsing of employees and users can choose a filtering service via DNS and sleep peacefully. In particular, the user should make sure that the service has these features:
» Frequent updating of blacklists, those lists where sites that should absolutely be avoided end up, and ensuring low latency (the time between requesting and “getting” the site)
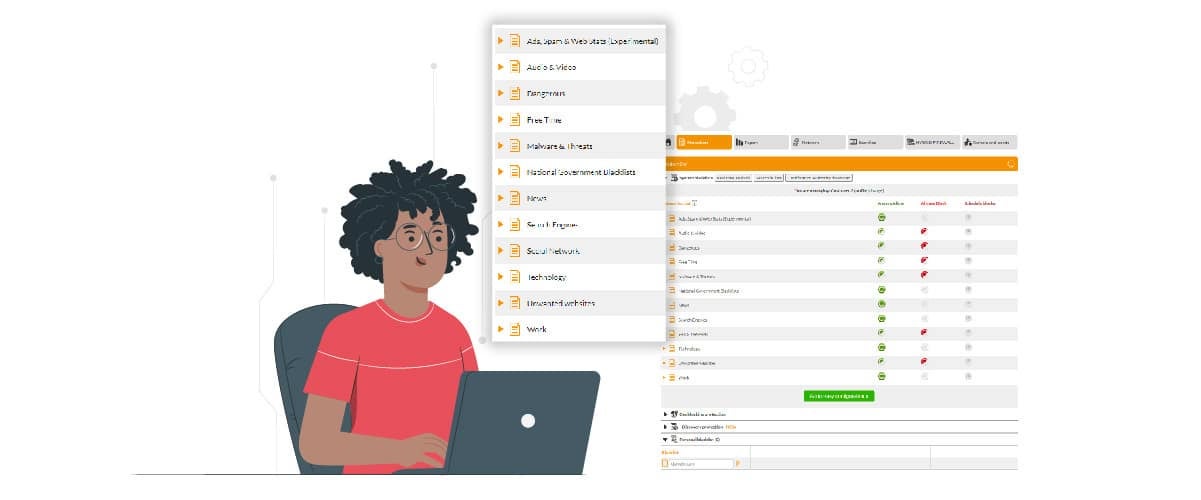
» Ability to customize the filter based upon your site blocking needs
» Ample categorization of malicious sites, as well as geoblocking, a blocking service based upon where the site resides which excludes countries considered to be dangerous from blacklists
» Use of artificial intelligence for higher quality blacklists, thereby avoiding the blocking of “clean” sites.
» Ease of configuration and customization (possibly paid for by a certified partner of the DNS filter maker).
>> FlashStart protects you from a wide array of threats and blocks access to malicious sites ? Request a quotation or try it now
FlashStart’s DNS filtering supports as many as eighty-five different content categories and claims a very low minimum latency. It also uses artificial intelligence algorithms to speed up the collection of data on DNS, domains and contents, “learning” from analysis of sites and predicting which others may be at risk of being blocked.
Partners around the world who offer FlashStart’s DNS filter all agree that the ease of configuration and customization of the service is one of its key features. FlashStart’s DNS filter also natively integrates with Microsoft’s Active Directory for immediate installation on corporate networks. Furthermore, it provides worldwide LAN protection and roaming on end points through the Anycast network.
Finally, the FlashStart filter ensures protection from attacks on corporate networks at a highly competitive price, which is lower than many of the security solutions which most small and medium-sized companies, ultimately, do not need. After all, if you protect your employees’ browsing, you are already in a very good position.
>> FlashStart is a leader in the field ? Request a quotation or try it now
You can activate the FlashStart® Cloud protection on any sort of Router and Firewall to secure desktop and mobile devices and IoT devices on local networks.