How to protect privacy on the Internet with DNS-over-TLS
1. Introduction to DNS over TLS (DoT)
Security and online privacy have become crucial concerns in the digital age. In this context, DNS-over-TLS (Domain Name System over Transport Layer Security), abbreviated as DoT, has emerged as an essential tool to protect our personal information and online activities.
To understand the importance of DoT, we must first grasp how the traditional DNS resolution system works. DNS, or Domain Name System, is the backbone of internet browsing, responsible for translating the web addresses we enter into our browsers into IP addresses needed to locate web servers and other online resources. However, the conventional DNS resolution process is vulnerable to various threats.
DNS-over-TLS (DoT) addresses these vulnerabilities by providing an additional layer of security and privacy. Essentially, DoT encrypts DNS queries and responses between the user’s device and the DNS server, ensuring that DNS requests travel securely over encrypted channels. This prevents attackers from intercepting or tampering with DNS information, providing a robust defense against eavesdropping and malicious manipulation.
The adoption of DNS-over-TLS can be advantageous for both individual users and businesses and organizations. For individuals, it represents an effective way to protect their online privacy, preventing internet service providers, governments, or other malicious entities from tracking their web activity. Companies and organizations can use DoT to enhance the security of their network infrastructure, minimizing the risk of DNS poisoning attacks and improving the integrity of their online communications.
>> FlashStart protects you from a wide range of threats and prevents access to malicious websites Request a quotation or try it now
2. The Risks of Unencrypted DNS Resolution
One of the most apparent risks of unencrypted DNS is data interception. Because DNS requests and responses are transmitted in plain text, malicious third parties can intercept and capture this information as it travels across the network. This means that details of visited web pages, used applications, and more can be collected and used to create user profiles or track online activities. This raises significant concerns regarding privacy and the security of personal information.
In traditional DNS, information travels in plain text, which means malicious third parties can intercept and eavesdrop on DNS requests, gaining valuable insights into your online activities. This includes knowledge of the websites visited, applications used, and other data that could be used for user profiling or cyber espionage. The lack of DNS encryption also opens the door to malicious manipulation of DNS responses, which can redirect users to fake and dangerous websites.
Another significant risk is malicious manipulation of DNS responses. Attackers can redirect users to fake and dangerous websites by altering DNS responses. This phenomenon is known as DNS poisoning and can have serious consequences, such as exposure to phishing sites designed to steal sensitive information like passwords and financial data.
Furthermore, unencrypted DNS exposes users to government censorship and surveillance. Governments and authorities can intercept DNS requests and block access to websites and online services with content they deem inappropriate or contrary to their policies.
>> You can install the FlashStart® Cloud protection on all sorts of Routers and Firewalls to secure your desktop and mobile devices as well as IoTs devices on local networks are safe from cyber threats
3. Why Configure DNS over TLS on the Network?
As we discussed earlier in this post, DNS security is one of the factors to take into consideration when talking about security; we can rely on different systems, but remember that DNS travels unencrypted on the network.
In this context, configuring DNS-over-TLS (DoT) on your network is a crucial measure to strengthen security and protect the privacy of all connected devices.
4. Why Businesses Should Adopt the DNS over TLS Protocol
» Improvement in Security: protecting DNS communications is essential for data security and preventing online threats.
» Improvement in Reputation: providing secure DNS services can enhance a company’s reputation among privacy-conscious customers.
» Regulatory Compliance: in some sectors, such as healthcare or finance, there are regulations that require data protection, including DNS traffic.
» Risk Reduction: adopting DNS Over TLS (DoT) helps reduce risks associated with DNS traffic manipulation and man-in-the-middle attacks.
5. Why Businesses Should Adopt the DNS over TLS Protocol
FlashStart offers a powerful Web content filtering solution that allows you to control and monitor access to Web sites from your network. You can set custom access policies, block malicious, inappropriate or unwanted websites and ensure that employees or users have access only to safe and relevant content. This is essential for maintaining network productivity and security. But not only that, FlashStart can offer several competitive advantages, such as remote agents to protect even off-site employees, local dnsproxy for ultra-low latency resolution, dns-cache, and customization and import of RPZ lists.
5.1 Protection from threats and malware in real time.
Cybersecurity is a priority, and FlashStart helps you protect your network from malware and threats in real time. Using advanced detection and analysis technologies, FlashStart proactively blocks malicious websites, dangerous downloads and online threats, preventing them from penetrating your network and compromising the security of your devices and data. This analysis is thanks to our AI, which instead analyzes possible attacks and unusual behavior to detect them in real time, without waiting for a database or signature update, as antivirus systems do.
5.2 Application control.
FlashStart allows you to manage and control applications running on your network. Policies can be set to restrict or allow certain applications, which is essential to prevent unauthorized use of applications that may pose a security risk or to maintain quality of service on the network.
5.3 Detailed reporting and analysis.
Visibility is critical to network security management. FlashStart provides detailed reports and analysis that allow you to monitor network traffic, identify potential threats, and assess compliance with security policies. This helps you make informed decisions and modify your security policies as needed.
5.4 Simple implementation.
FlashStart integrates easily into existing network infrastructure. Implementation is non-invasive and does not require expensive hardware or significant changes to the network configuration. This means you can effectively protect your network without unnecessary hassle and at low cost.
5.5 Regulatory compliance.
FlashStart helps you comply with regulations and security standards, which is essential in environments where regulatory compliance is required. You can set custom policies to meet specific requirements and maintain detailed records of activity on the network.
Learn about all the features FlashStart offers to protect your network and prevent Internet attacks.
6. Does FlashStart support DNS-over-TLS?
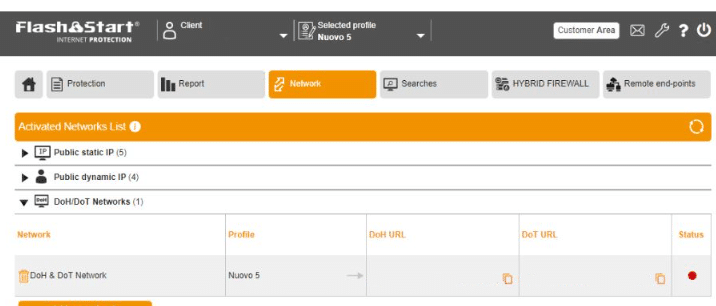
With the new version 4.0, among its major enhancements, DOT support has been added to our solution; now not only will you have the security levels discussed above, but you can also configure your network to adopt DOT and increase network security.
Using FlashStart’s ClientShield, all packets used to be closed within a secure VPN connection.
Now, with the new DNS over TLS feature, all requests are made natively under this protection: all processes are encrypted and certified by the SSL/TSL protocol, making them safe from malicious attacks.
7. Why FlashStart Chose to Adopt DNS over TLS
DNS over TLS has been an industry standard since 2018. It is cross-platform and natively supported by major operating systems, including mobile ones like iOS and Android. FlashStart has chosen to adopt DNS over TLS for its numerous advantages, to improve network integrity, and, most importantly, for security. Specifically, here are some of the strengths of DNS over TLS:
7.1 Strengthening Online Privacy
The main reason for configuring DNS-over-TLS on the network is to strengthen online privacy. In traditional DNS, queries and responses are transmitted in plain text, which means malicious third parties, such as Internet Service Providers (ISPs) or government entities, can intercept and eavesdrop on these communications. DoT, on the other hand, encrypts DNS queries and responses.
7.2 Improved Security
In addition to privacy, security is a crucial concern in the cyber world. Traditional DNS is exposed to risks such as DNS poisoning, which can redirect users to malicious websites. By configuring DNS-over-TLS, the risk of such attacks is significantly reduced, as DNS responses are securely provided through encrypted channels. This prevents malicious manipulation of DNS responses and enhances the integrity of online communications.
7.3 Protection of Personal Information
In a world where personal information is valuable and often susceptible to collection for targeted advertising purposes, protecting your data is of paramount importance. Unencrypted traditional DNS can expose the details of your online activities to third parties. With DNS-over-TLS, your personal information is kept confidential, making it difficult to create unwanted user profiles or track your online habits.
7.4 Resilience Against Censorship and Blocking
DNS-over-TLS can be a valuable tool for those dealing with online censorship. The encryption of DNS requests prevents authorities from blocking or restricting access to websites and online services. This is particularly important in regions where freedom of expression is threatened and information is subject to censorship.
7.5 Easy Implementation on Multiple Devices
Configuring DNS-over-TLS is not a complex operation and can be done on a variety of devices, including computers, mobile devices, and routers. Specific instructions may vary depending on the operating system or device, but the implementation of DNS-over-TLS is accessible to most users, making online security more achievable than ever.
7.6 Adaptability to Public and Private Networks
DNS-over-TLS is versatile and adapts to both public and private networks. If you use public Wi-Fi networks in bars, airports, or other places, configuring DoT on your devices will provide an additional layer of security and privacy on these potentially insecure networks.
>> A filter solutions software can protect the household of your employees working remotely and thus, indirectly, also your company. FlashStart is totally cloud-based and easy to activate ? Request a quotation or try it now
8. Summary
In short, DNS-over-TLS (DoT) is a security protocol designed to encrypt DNS queries and responses, safeguarding online privacy and integrity of communications.
It helps prevent unauthorized surveillance and data manipulation by encrypting DNS traffic, making domain name resolution requests more secure. DNS-over-TLS is essential for strengthening online security and privacy, protecting against threats such as DNS poisoning and ensuring the safeguarding of personal information and online activities.
It can be configured on a variety of devices and operating systems, making it a convenient tool for individual users and organizations looking to protect their networks and online data. You already have the integration of FlashStart to enhance the security of your network.
I hope this new post has helped you understand the general concepts and security implications of DNS services.
See you in the next post!
>> FlashStart protects from a wide range of threats and prevents access to malicious websites ? Start your free trial now and request a quote
You can activate the FlashStart® Cloud protection on any sort of Router and Firewall to secure desktop and mobile devices and IoT devices on local networks.